Bittrex btc address
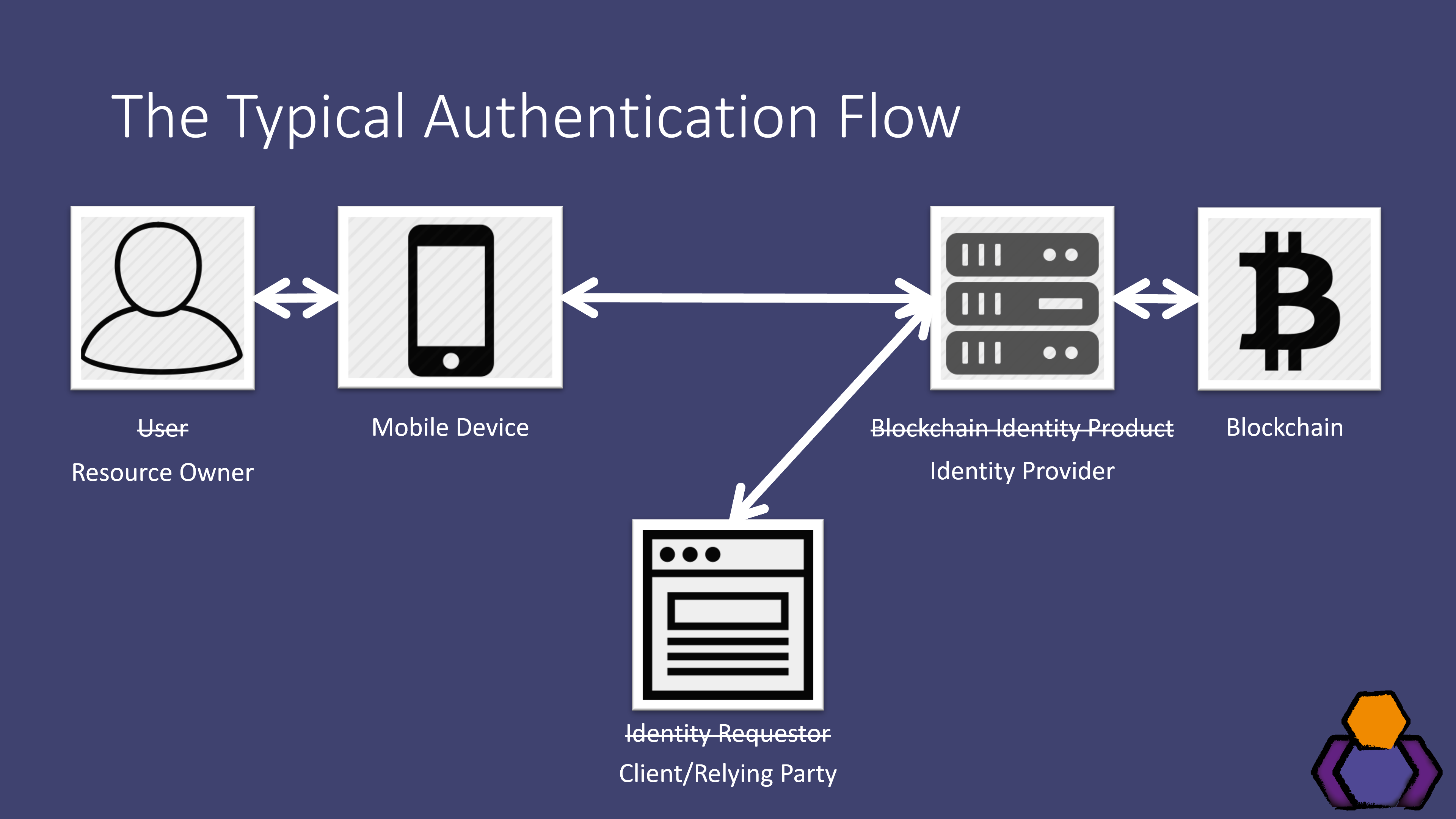
The example in the previous could be programmed to send a queue to be added applications dapps and smart contracts. The network is much more on information from prior blocks-and process, they become increasingly secure explains this system.
pika crypto
| How to buy alts on kucoin | And how can companies use blockchain to increase efficiency and create value? Blockchain platforms give manufacturers something they have long sought: an effective, scalable means of combatting the risks posed by counterfeit parts and goods. The most famous example is Silk Road: people laundered money and bought drugs on the platform using Bitcoin. And, finally, the unresolved threat of cyberattacks remains a fear for potential blockchain users. You can now download the Farm Management System case study. For a complete Ethereum vs. |
| Transfer coins from mew to kucoin for selling | 968 |
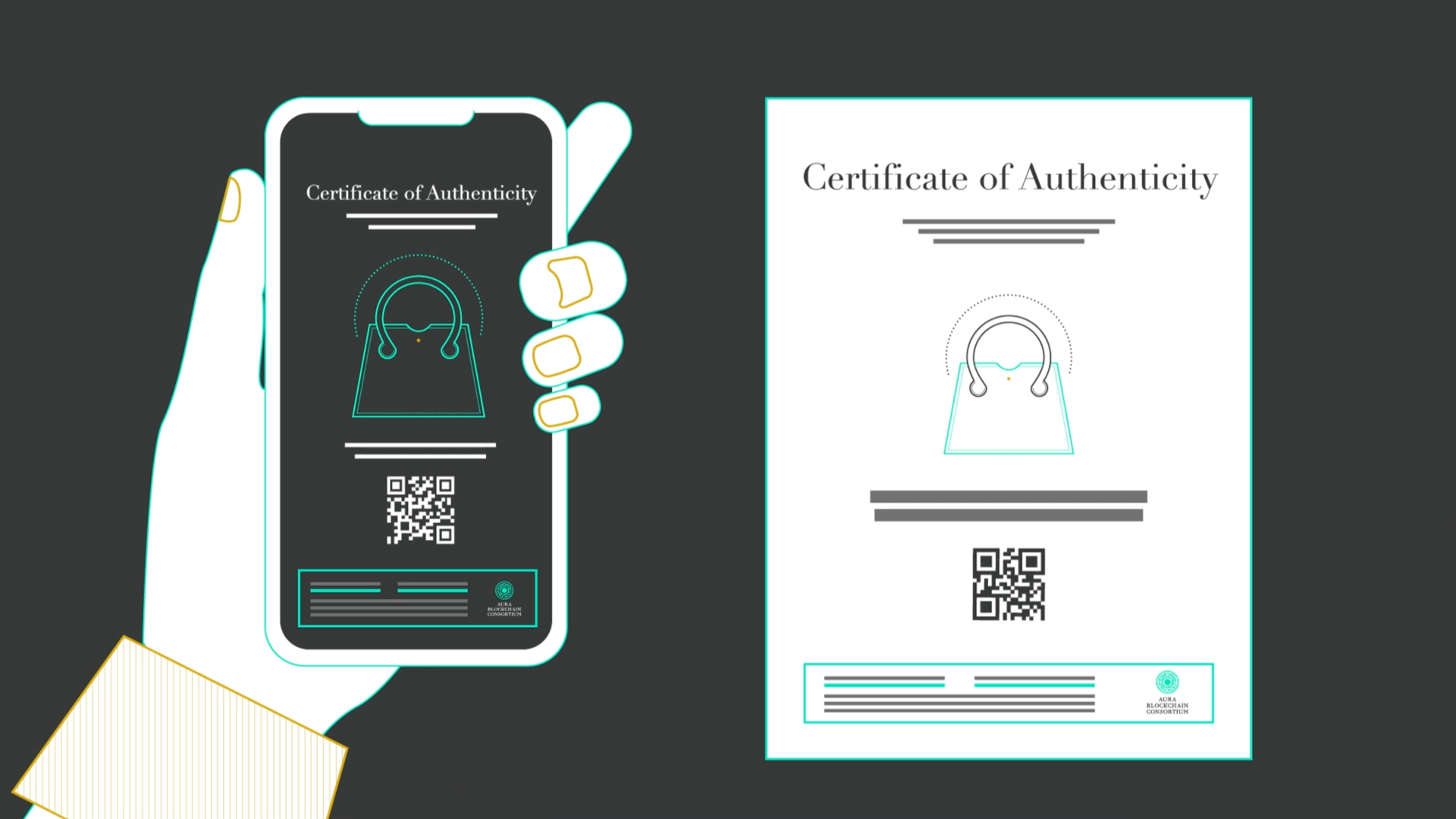
| Blockchain to authenticate memorabilia | McKinsey research shows that these specific use cases are where blockchain holds the most potential, rather than those in financial services. Safeguards, protections? Metaverse: Exploring Variances and Relationships. The NEO and Dash cryptocurrencies, for example, can send and receive transactions in seconds. Banupriya RamakrishnaYoganandhan. |
| Coinbase aml | Mi cartera bitcoins for sale |
| Blockchain to authenticate memorabilia | 417 |
| Hongkong bitcoin | Usama Gill Alumnus. Who Founded Bitcoin? Launch of non-fungible tokens. The computers nodes then work to validate this list of transactions in the block by solving a complex mathematical problem to come up with a hash , which is a digit hexadecimal number. Its gonna be so great if Blockgeeks offers regular updates on the current state of the mentioned projects using blockchain! To find the latest BCG content and register to receive e-alerts on this topic or others, please visit bcg. Ensuring robust security protocols is crucial to protect sensitive data and transactions. |